Understand GPS Spoofing Mechanics Thoroughly
Learn How to Prevent a Severe GPS Hack Today
Navigation systems fail entirely when malicious radio signals overpower authentic satellite broadcasts. Anyone seeking to understand what is GPS spoofing must first look at radio frequency manipulation. Fake transmitters force receivers to calculate completely wrong coordinates or timing data. Devices blindly trust these incoming forged transmissions without immediate verification.
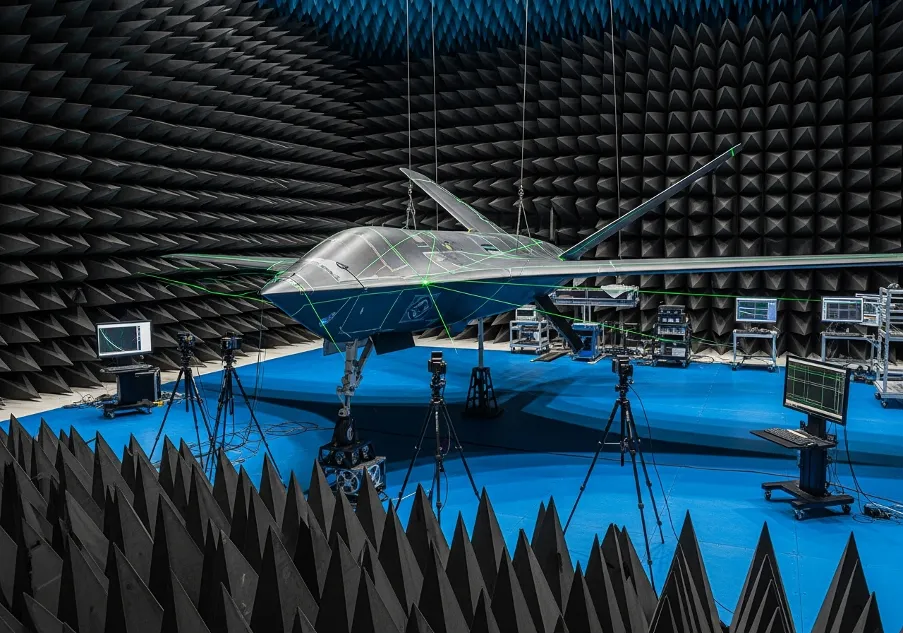
This hardware manipulation differs drastically from simple jamming that merely drops the satellite connection. Sophisticated GPS spoofing attacks feed highly deceptive raw data directly to the target hardware matrix. Cargo ships, military drones, and consumer smartphones absorb these synthetic signals. The target object physically shifts off course while internal displays show normal routing.
The Core Mechanics of Signal Overpowering
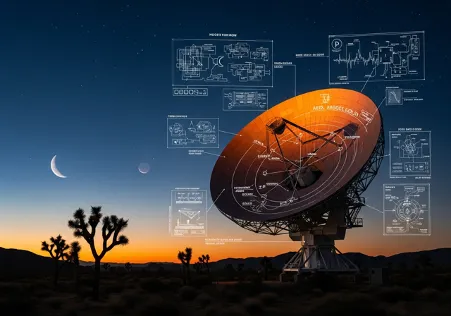
Hardware manipulation relies heavily on overpowering incredibly weak space-based signals. A basic location spoofer broadcasts stronger radio waves locally to hijack the target receiving antenna. The navigation chip naturally locks onto the loudest and clearest transmitter nearby. Authentic signals traveling from orbit simply cannot compete with ground-based amplifiers.
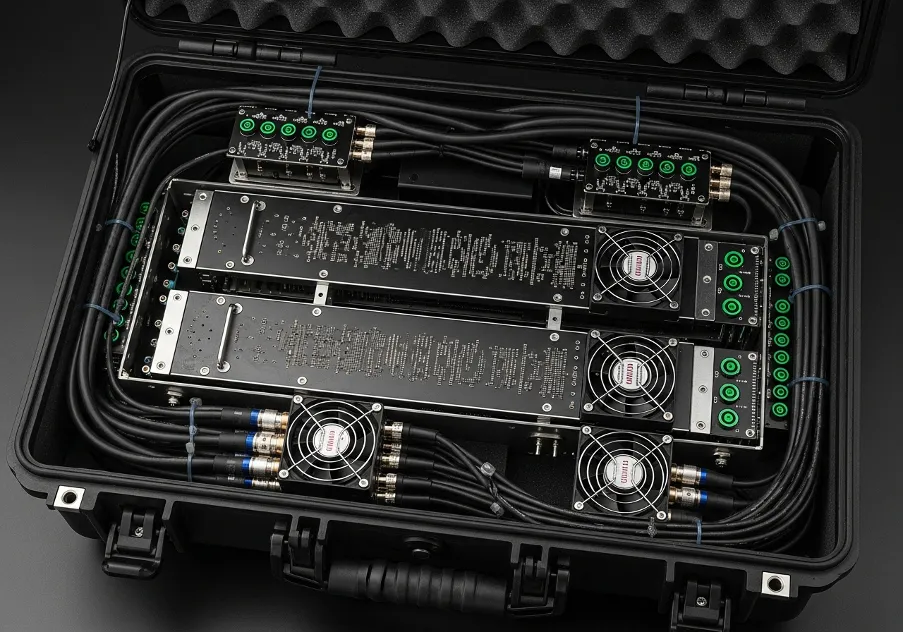
Attackers deploy specific hardware components to execute a successful GPS spoof against modern navigation targets:
software defined radios generating false satellite transmission codes;
RF power amplifiers boosting the synthetic radio waves significantly;
directional high-gain antennas focusing the transmission precisely.
These combined parts create a localized deception zone effectively. Executing spoofing GPS tactics requires flawless timing and strict satellite data synchronization. If the local timing mismatches the global constellation, the receiver throws an immediate error.
The overall operational impact of location spoofing forces the target device to report fabricated coordinates. Drone operators might see their equipment hovering miles away from reality. The flight controller hardware remains completely unaware of the ongoing radio manipulation.
Executing the Signal Takeover Process
The initial attack phase often utilizes a subtle "carry-off" technique. People asking how does GPS spoofing work usually miss the critical signal-to-noise ratio matching phase. The malicious transmitter aligns its false signal perfectly with the authentic satellite broadcast. This alignment prevents sudden jumps in coordinate calculations.
Once fully aligned, the unauthorized transmitter slowly increases its power output. Many modern GPS spoofers automate this power shift algorithmically to avoid triggering loss-of-lock software alarms. The target receiver smoothly transitions its focus to the fake data stream. Operators notice absolutely zero disruption during this handoff phase.
Attackers then gradually alter the time or geographic position data. Anyone wondering what is location spoofing at a technical level should analyze this slow coordinate drift. The target ship or vehicle physically moves toward a new destination unknowingly. The autopilot steering follows the fake waypoints precisely.
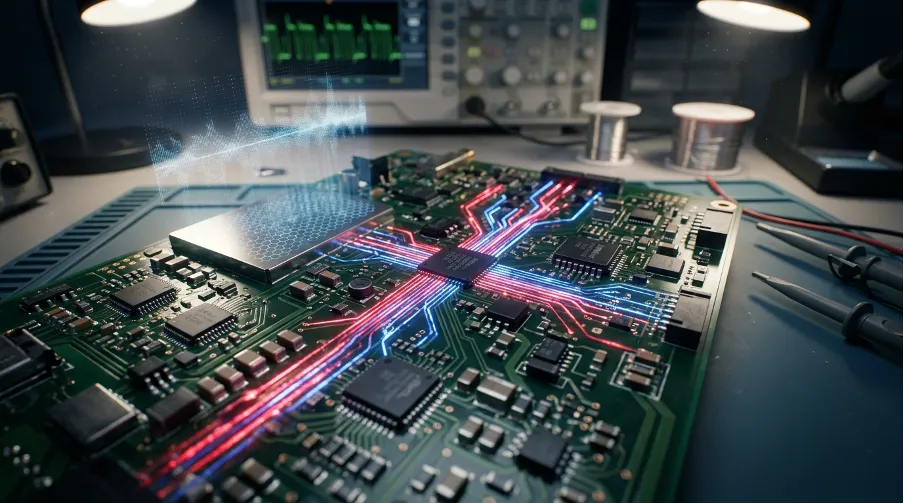
Commercial software defined radios made these exact attacks highly accessible recently. Open-source Python scripts replace expensive military hardware for generating false satellite signals. The barrier to entry for manipulating global coordinates dropped significantly for amateur hackers.
Regulatory Repercussions and Detection Hardware
Tampering with aviation or maritime navigation networks creates massive public safety hazards. Users asking is GPS spoofing illegal will find strict federal broadcasting laws strictly prohibiting such interference. Regulatory bodies heavily penalize unauthorized radio frequency transmissions globally.
Authorities classify unauthorized radio frequency interference as a severe federal offense:
- disrupting commercial aviation routing and landing systems;
- interfering with critical maritime tracking and steering networks;
- manipulating emergency responder location dispatch data.
Enforcement agencies utilize triangulation networks to track down these illicit transmitters quickly. For those wondering is location spoofing illegal, the Federal Communications Commission issues massive financial fines and actual prison sentences. The legal risks far outweigh any perceived tactical benefits.
Hardware detection heavily relies on analyzing specific time-of-arrival metrics. Understanding what is a GPS spoofer helps security engineers design better authentication protocols like WAAS message verification. Implementing stronger cryptographic encryption defends infrastructure against these deceptive radio broadcasts.
Target Vulnerabilities and Equipment Availability
Consumer smartphones severely lack robust hardware defense mechanisms against forged radio signals. A localized location spoof forces mobile applications to display incorrect map coordinates instantly. Delivery drivers sometimes manipulate their internal tracking data using similar concepts.
Security researchers continually study these hardware vulnerabilities to build stronger receiver chips. Manuals detailing how to GPS spoof exist on specialized cybersecurity forums for authorized penetration testing purposes. White-hat engineers test critical power infrastructure against these exact radio vulnerabilities.
Maritime navigation systems remain highly susceptible to a targeted GPS hack out in open ocean waters. Massive cargo ships relying entirely on automated steering protocols drift off course easily. Captains must actively cross-check electronic coordinates with traditional radar and visual landmarks.
Building a highly functional GPS spoofing device requires only a standard laptop and a HackRF transmitter. The open-source development community provides the exact code repositories for generating the L1/L2 satellite signals. This technical simplicity alarms national security agencies monitoring critical infrastructure.
Global Impacts and Countermeasure Engineering
International tech communities encounter these specific technical terms in various localized contexts. Security blogs explain the spoofing meaning in telugu as digital deception using radio frequency manipulation. The core scientific concept remains completely identical across all engineering languages.
Mobile gamers frequently attempt to spoof location coordinates for augmented reality mapping games. They typically use software mock locations rather than actual radio frequency transmitters. This pure software trickery differs entirely from authentic hardware-level signal forging.
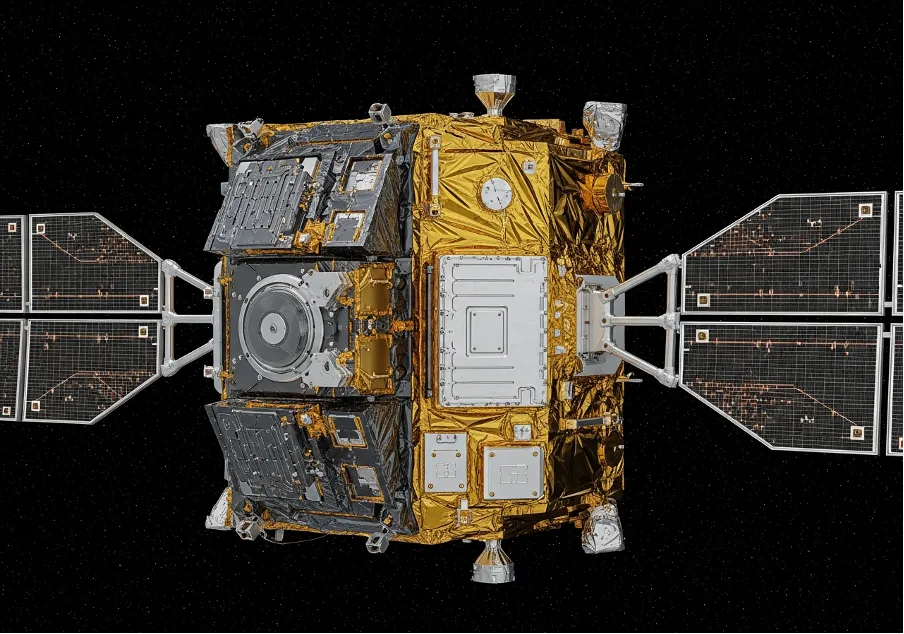
Critical national infrastructure requires exact atomic timing data from satellite clocks. A successful GPS-spoofing campaign disrupts power grid phase synchronization and cellular tower data handoffs. The structural damage extends far beyond simple digital map routing errors.
Defense engineers implement complex multi-antenna arrays to detect incoming signal direction anomalies accurately. Surviving a dedicated GPS attack requires resilient hardware that cross-references multiple satellite constellations simultaneously. Incorporating Galileo and GLONASS data streams provides crucial redundancy during heavy interference events.
Trusted Worldwide
Operating in more than 50 countries, we provide cutting-edge defense solutions that ensure your safety to every corner of the globe.
Get Advice From Our Experts
Please complete the feedback form to gain exclusive access to our catalog showcasing models that are not available on our website
We’re here to assist you with any inquiries, support, or information you need. Whether you're interested in our defense products, looking to collaborate, or simply have a question, our team is ready to help.