Cyber Range Platform Deployment
Integrating Cyber Range Tools Effectively
Security operations centers (SOC) face automated threats that outpace standard training protocols, leaving analysts unprepared for live ransomware breaches. Traditional static tutorials fail to replicate the complex telemetry generated during actual IT and OT infrastructure attacks.
Transitioning to interactive, live-fire environments allows incident responders to encounter precise replicas of enterprise networks before a true breach occurs. Implementing a dedicated cyber range forces security teams to build muscle memory under extreme technical stress.
Architecture of Simulated Environments
To recreate a corporate network accurately, a cyber range platform must orchestrate virtual machines, routers, and endpoint agents identical to the production environment. Engineers deploy active directory forests and load balancers to ensure the cyber range simulation mirrors reality perfectly.
Operators inject malicious traffic directly into these cloned segments to observe how analysts detect anomalies using native monitoring software. Integrating specific cyber range tools ensures that instructors capture participant keystrokes and system responses for immediate post-incident analysis.
A robust cyber range solution incorporates commercial firewalls and SIEM systems, rather than generic emulators, forcing defenders to write actual detection syntax. When updating internal apps, cyber range environments isolate the experimental code from production networks to prevent accidental disruption.
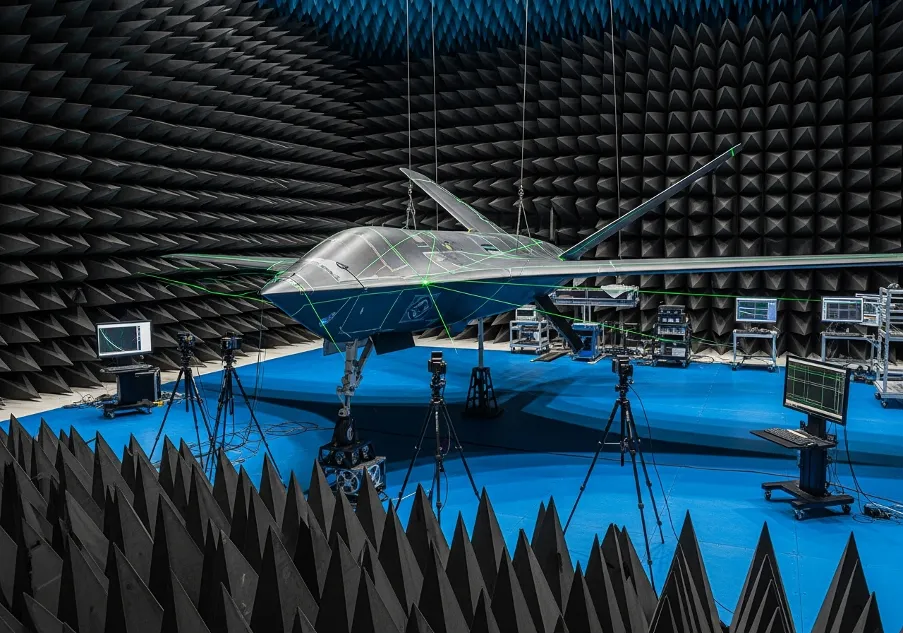
Deployment and Operational Scenarios
Preparing for a targeted attack requires security personnel to execute a structured cyber range exercise based on recent threat intelligence reports. Teams confront simulated adversaries performing lateral movement, requiring defenders to isolate compromised nodes and mitigate the breach without halting operational technology.
During live-fire testing, network architects mandate specific diagnostic protocols:
- configuring packet capture sensors to trace lateral movement across subnets;
- extracting forensic artifacts from compromised endpoints during the attack sequence;
- tuning SIEM correlation rules to block automated exfiltration scripts.
Executing a full-scale cyber drill validates the existing incident response playbook and highlights gaps in cross-departmental communication. Organisations depend on specialized cyber range software to measure response times and calculate the precise impact of delayed remediation.
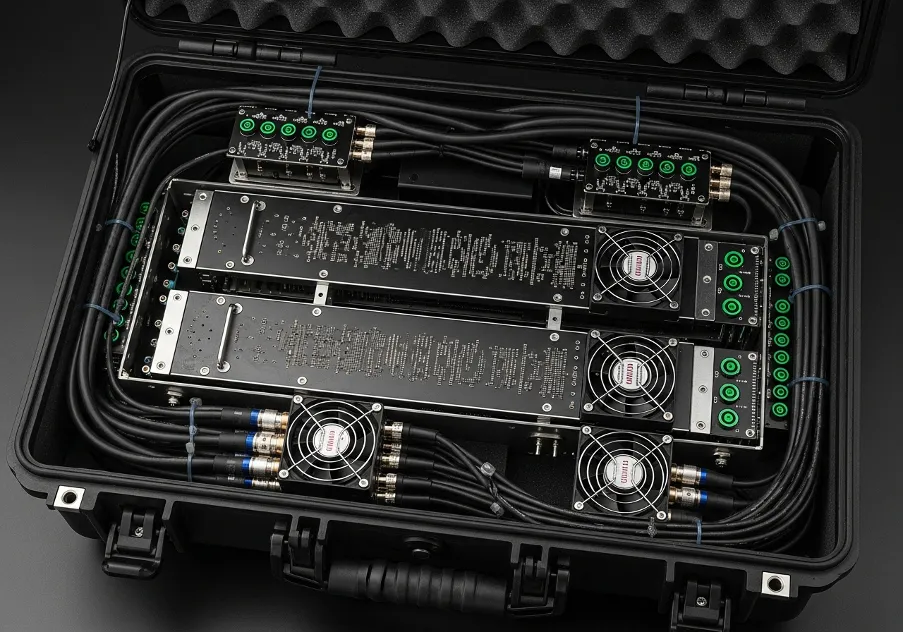
Vendor Ecosystem and Cloud Adoption
Maintaining an on-premise emulation datacenter demands significant hardware investment and continuous threat signature updates from internal engineering staff. Shifting toward an online cyber range model eliminates the physical infrastructure requirement, enabling remote SOC teams to access scenarios through a secure browser connection.
Multiple cyber range companies deliver pre-configured attack environments tailored to financial, industrial, or healthcare network architectures. Specialised cyber range providers like SimSpace and Cyberbit build high-fidelity replicas to evaluate security personnel during complex hiring assessments.
The transition to cyber range as a service allows rapid provisioning of specific tabletop scenarios without modifying internal corporate hardware. This cloud-based delivery model provides instructors with instant access to dynamic virtualisation clusters.
Advanced Virtualised Infrastructures
By aggregating native cyber range services, solutions, applications, network architects build unified threat mitigation protocols across isolated network segments. A single cyberrange instance might combine containerised workloads and legacy mainframes to replicate a fragmented corporate structure accurately.
To maintain defensive readiness, administrators routinely alter the core simulation parameters:
- deploying virtual firewalls identical to the hardware securing the external perimeter;
- orchestrating simulated user traffic to mask the presence of malicious payloads;
- assessing defensive configurations against polymorphic malware variants.
Analysing these metrics allows instructors to adjust the difficulty of incoming attacks dynamically based on the trainees' real-time performance. Utilizing integrated cyber ranges ensures that every analyst action registers within the centralized evaluation matrix for automated scoring.
Strategic Integration and Budgeting
Financial planning for simulation environments depends heavily on the volume of concurrent users and the complexity of the replicated enterprise network. The baseline cyber range cost fluctuates widely, typically scaling from $10,000 to $100,000 annually based on the required computing resources and scenario fidelity.
Enterprises must scrutinize the technical parameters offered by niche European providers like Protelion or DIATEAM to meet regional data compliance standards. Selecting the right combination of simulation nodes guarantees that the infrastructure investment translates directly into reduced breach remediation times.
Trusted Worldwide
Operating in more than 50 countries, we provide cutting-edge defense solutions that ensure your safety to every corner of the globe.
Get Advice From Our Experts
Please complete the feedback form to gain exclusive access to our catalog showcasing models that are not available on our website
We’re here to assist you with any inquiries, support, or information you need. Whether you're interested in our defense products, looking to collaborate, or simply have a question, our team is ready to help.