GPS Spoofing Explained
How Hackers Use a Fake GPS to Reroute Ships
Navigation systems completely rely on accurate satellite data to function properly. The rising threat of GPS spoofing creates massive vulnerabilities for commercial aviation and personal devices alike. Unlike basic signal blocking, this specific attack feeds counterfeit coordinates directly to a receiver. GPS spoofing forces hardware to calculate incorrect geographic positions.
Many people confuse this tactic with GPS jamming, but they operate entirely differently on a technical level. Criminals actively manipulate spoofing GPS signals to silently hijack navigation paths without triggering immediate alarms. Location spoofing makes defense much more complex for engineers. Fake GPS signals look perfectly real to standard unmodified equipment.
The Mechanics of False Signals
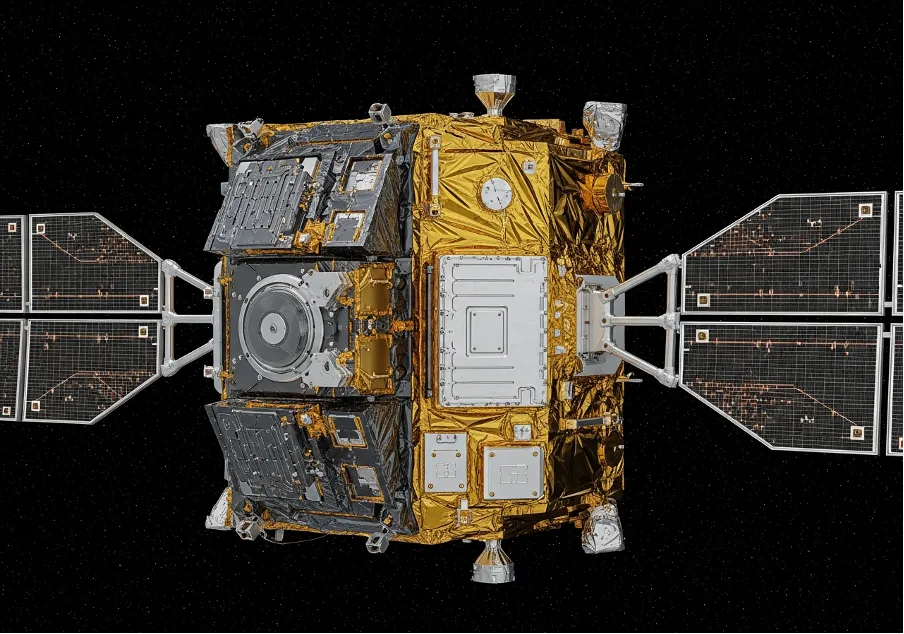
Satellites broadcast incredibly weak navigation signals from orbit down to Earth. A malicious location spoofer exploits this physical limitation by broadcasting a much stronger local radio frequency. The targeted receiver naturally abandons the legitimate satellite lock to follow the louder signal. This process forms the core mechanic of all GPS spoofing operations.
Engineers observe specific sequential stages when a GPS spoof attack begins:
- the transmitter generates a synchronized counterfeit signal locally;
- the target device accepts the fake GPS data as authentic input;
- the user interface slowly displays incorrect navigation metrics and routes.
The internal hardware inside a standard receiver cannot easily distinguish these false inputs. Any basic GPS spoofer overrides the baseline 1575.42 MHz L1 frequency completely. This manipulation forces the device to calculate a completely wrong geographical location. Advanced GPS spoofing equipment essentially blinds the receiver to physical reality.
Equipment and Signal Overpowering
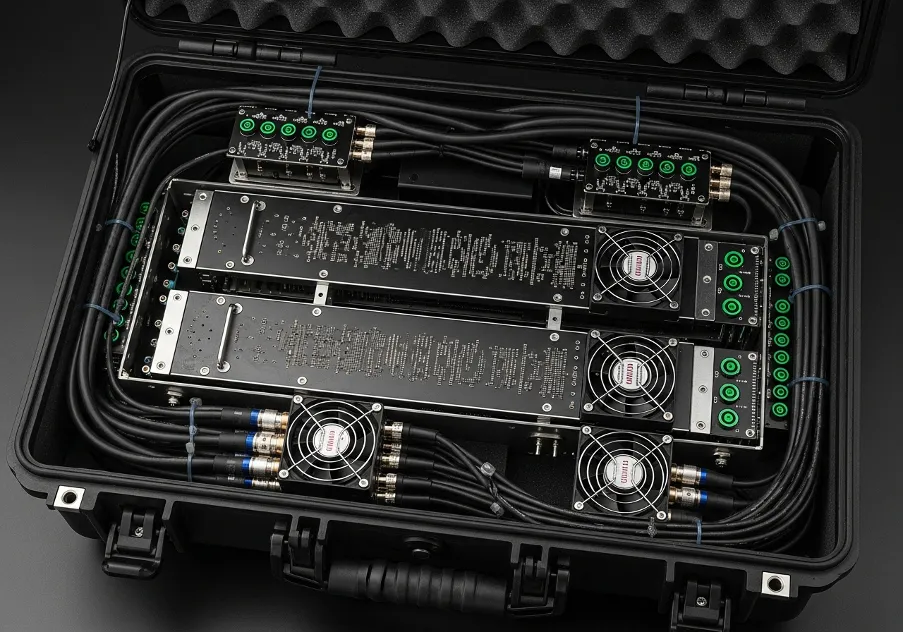
Hackers build these interference setups using software-defined radios and open-source code repositories. They disrupt GPS live tracking systems with relatively cheap commercial equipment bought online. A targeted transport device instantly recalculates its entire route based on the new data. Execution requires very little technical expertise due to accessible hardware today.
Personal devices also face severe risks from direct internal software manipulation. Mobile users often install tools to spoof location data for gaming advantages or strict privacy controls. Android devices require developer mode activation for this coordinate manipulation to work properly. These modified applications override the real hardware sensor readings entirely.
Jailbroken iOS systems allow similar unauthorized core system modifications by users. A dedicated GPS location spoofer app overrides the internal API coordinates completely. Regular applications then read this location spoofing output as hard factual baseline data. Manipulating coordinates on mobile phones breaks weather alerts and mapping tools entirely.
Critical Risks for Industries
Transportation networks face severe operational hazards from these continuous signal attacks. A simple GPS jam attack just breaks connectivity, but fake signals cause massive ships to alter course. Commercial flights enter restricted airspace unknowingly due to these silent broadcast tactics. The risk of physical collision increases dramatically under manipulated navigation conditions.
Specific sectors suffer unique financial damages from counterfeit aero GPS navigation data:
- maritime logistics face hijacked cargo routes across oceans;
- financial markets lose precise microsecond live GPS time synchronization globally;
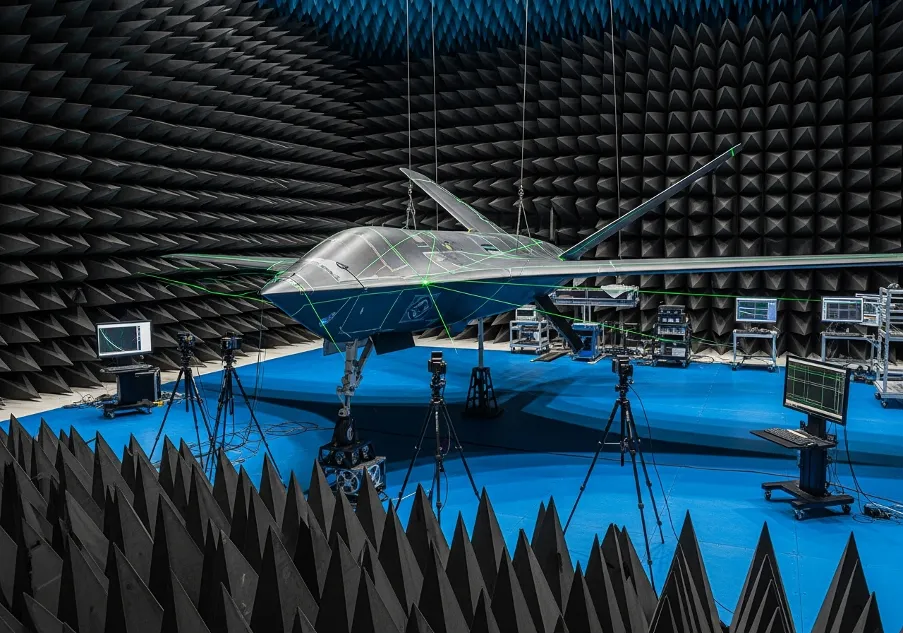
- military drones receive manipulated terrain coordinates during critical missions.
State actors frequently deploy advanced GPS spoofers to protect highly sensitive installations. They redirect unauthorized drones away from military bases or vital government buildings. This tactical defense mechanism heavily impacts civilian airspace nearby with strong fake signals. Strategic signal manipulation serves as an invisible electronic defensive shield.
Tracking the Disruption
Aviation authorities constantly monitor global navigation interference to ensure daily passenger safety. Pilots report coordinate anomalies to update a central GPS outage map for regional flight planning. These databases show real-time signal disruptions across major military conflict zones. Commercial airlines immediately reroute traffic away from these dangerous broadcast areas.
Maritime organizations track similar electromagnetic anomalies over open international waters. Analyzing a detailed GPS jamming map helps captains plan alternative manual navigation routes safely. They rely on celestial tracking or inertial reference systems instead of vulnerable digital screens. Accurate digital data sharing prevents massive cargo ships from running aground.
Network engineers analyze signal degradation patterns across entire affected continents continuously. A comprehensive GPS coverage map highlights dead zones caused by intensive military testing exercises. Airlines adjust their strict flight corridors based on these specific technical reports. Continuous spectrum monitoring keeps the global supply chain moving safely.
Predicting the next major attack vector requires massive localized sensor data collection. Security researchers deploy localized antennas to catch sudden coordinate jumps instantly. Rapid detection of digital interference minimizes the financial damage to global logistics companies. Manipulated data always leaves a specific digital footprint in the system.
Defense Strategies and Hardware
Protecting critical infrastructure requires advanced cryptographic verification of all incoming signals. Modern GPS spoofing detection relies heavily on multi-constellation cross-referencing algorithms. Receivers check Galileo or GLONASS data against the primary American system for discrepancies. If the satellite coordinates mismatch, the system flags a digital manipulation attempt.
Hardware upgrades include complex directional antennas and military-grade network encryption protocols. They block sudden location spoof attempts by mathematically analyzing the incoming signal angle. If the transmission comes from the ground, the anti-spoofing system rejects it entirely. Physical hardware defenses stop manipulated broadcasts before internal processor calculation begins.
Software algorithms also flag unrealistic speed jumps or sudden altitude changes. Immediate system alerts allow human operators to switch to backup inertial systems safely. Good cyber hygiene and updated receiver firmware remain critical software layers against attacks. Defeating digital broadcast manipulation requires constant technological adaptation and testing.
Learn more about alternative systems and related products from Prodefence.
Trusted Worldwide
Operating in more than 50 countries, we provide cutting-edge defense solutions that ensure your safety to every corner of the globe.
Get Advice From Our Experts
Please complete the feedback form to gain exclusive access to our catalog showcasing models that are not available on our website
We’re here to assist you with any inquiries, support, or information you need. Whether you're interested in our defense products, looking to collaborate, or simply have a question, our team is ready to help.