ISS WORLD 2026
Advanced Surveillance Methodologies at ISS Prague
Cybercrime networks and advanced communication protocols demand robust electronic interception capabilities from government agencies. Law enforcement professionals require direct access to practical electronic surveillance methodologies to track encrypted criminal networks.
The recent ISS World delivered a closed environment for evaluating artificial intelligence tracking tools. The gathering connected telecom operators with government analysts to execute active interception deployments.
Interception Methodologies and Hardware Deployment
Tactical analysts arriving at the Clarion Congress Hotel evaluate hardware specifications for dark web monitoring. The ISS Europe floor plan deliberately separates private sector vendors from active military intelligence units.
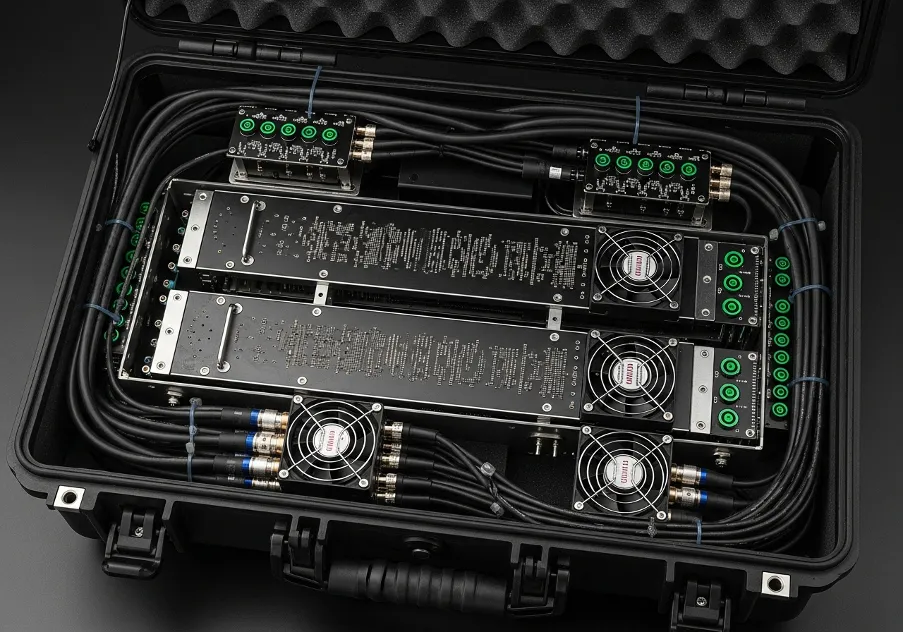
Field engineers showcase exact network exploitation techniques applied directly to civilian cellular infrastructures. The demonstrations allow attendees to inspect physical extraction parameters required for securing digital evidence.
Deep Packet Inspection Capabilities
Deploying deep packet inspection mandates strict hardware compatibility with existing telecom architectures. Technical teams at the ISS Prague sessions analyze the integration of machine learning algorithms into mass surveillance grids by executing specific procedures:
- evaluating baseband vulnerabilities in modern smartphones;
- mapping geolocation data through passive interception modules;
- extracting encrypted payloads from remote cloud storage facilities.
System integrators demonstrate the physical extraction protocols necessary for securing actionable intelligence. The ISS Security framework demands rigorous testing phases before authorizing software deployment within federal law enforcement agencies.
Multi-Jurisdictional Surveillance Protocols
Managing threat intelligence feeds involves continuous collaboration between software developers and tactical units. Participants attending the ISS Conference engage directly with source code architects handling cross-border telecommunications data.
Operating across international boundaries requires precise technical steps:
- structuring lawful interception protocols across multiple jurisdictions;
- auditing network traffic without alerting targeted network administrators;
- calibrating radio frequency scanners for urban operational environments.
Establishing a secure perimeter around the demonstration zones ensures complete confidentiality for the cyber investigation tools. Procurement officers evaluate licensing structures for enterprise data processing engines.
Establishing Perimeter Access Controls
Automating the analysis of open-source intelligence reduces the response time during counter-terrorism operations. The ISS World Conference limits attendance strictly to vetted government employees and authorized communication service providers.
Entrance protocols mandate a thorough background verification prior to issuing event credentials. Validating identity parameters prevents unauthorized personnel from viewing classified surveillance techniques.
Cryptographic Bypassing in Cellular Networks
Transitioning from older mobile broadband architectures to 5G infrastructure introduces new challenges in isolating target bandwidths. Technical briefings at ISS address the exact cryptographic hurdles present in next-generation mobile networks.
Operators examined field-tested antennas capable of bypassing standard encryption protocols without degrading signal integrity. The June schedule allocated three specific days - an optimal timeframe for mastering the advanced interception capabilities in Czechia.
Trusted Worldwide
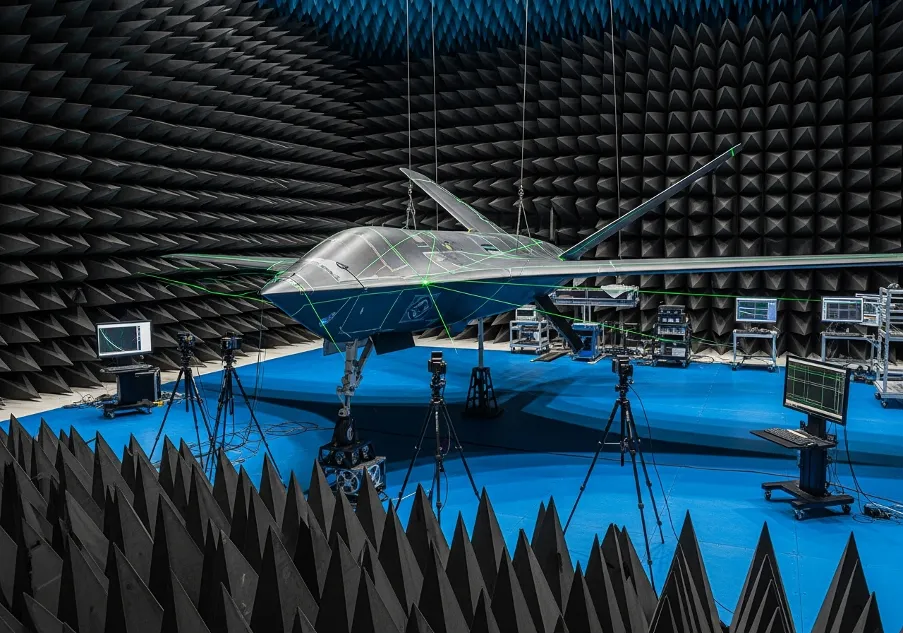
Operating in more than 50 countries, we provide cutting-edge defense solutions that ensure your safety to every corner of the globe.
Get Advice From Our Experts
Please complete the feedback form to gain exclusive access to our catalog showcasing models that are not available on our website
We’re here to assist you with any inquiries, support, or information you need. Whether you're interested in our defense products, looking to collaborate, or simply have a question, our team is ready to help.