What is Counter Surveillance
Deep Dive into Technical Surveillance Countermeasures
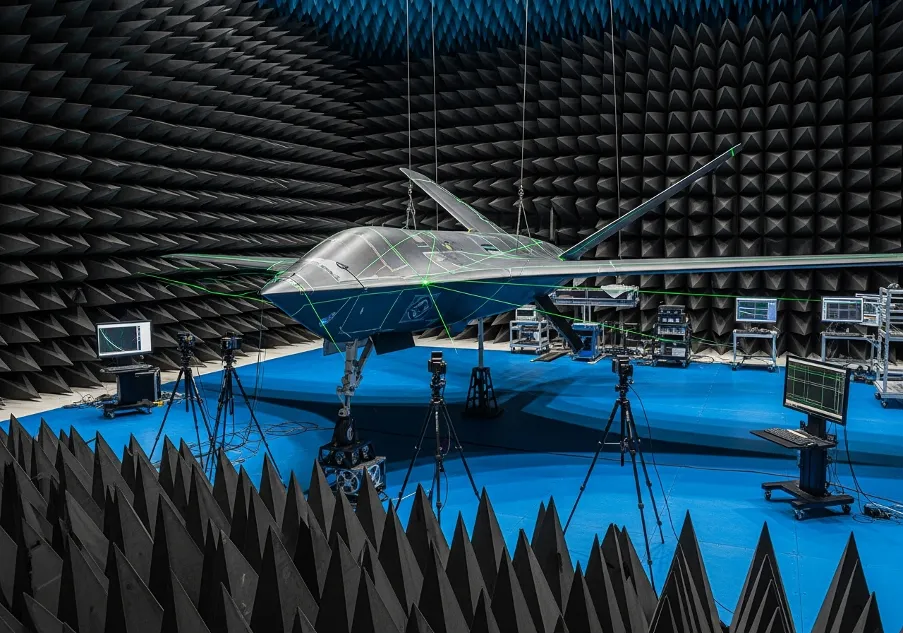
Corporate espionage and targeted monitoring compromise physical assets and digital privacy daily. Understanding what is counter surveillance requires analyzing covert audio transmitters, hidden optical lenses, and GPS tracking systems deployed by adversaries. Modern threat actors utilize sophisticated electromagnetic radiation emitters to intercept sensitive data streams. Executives and security personnel must deploy proactive countersurveillance protocols to identify and dismantle these monitoring attempts before critical information leaks occur.
Transitioning from passive awareness to active threat hunting involves mastering specific counter surveillance tactics. Defining the exact counter surveillance definition focuses on third party operatives actively detecting external monitoring efforts. The operational scope covers everything from physical detection routes to technical sweeps using non-linear junction detectors.
Establishing Baseline Security Protocols
Implementing effective counter surveillance measures demands a systematic approach to physical and digital environments. You must understand what is tscm to protect corporate boardrooms and private residences from advanced acoustic eavesdropping. Executing technical surveillance countermeasures involves physical inspections and electronic diagnostics to locate unauthorized bugs. Security teams execute physical checks on vehicles to find newly installed tracking hardware.
Professionals distinguish between general situational awareness and structured counter-surveillance. This framework detects optical devices and disrupts unauthorized data collection streams. Recognizing the interplay between surveillance and counter surveillance allows operatives to anticipate adversary positioning. Analyzing the threat landscape dictates the necessary equipment budget, typically ranging from 5000 to 25000 dollars for standard diagnostic hardware.
Technical Diagnostics and Electronic Sweeping
Hardware detection forms the core of technical counter surveillance measures. Operatives sweep premises using radio frequency detectors to locate active transmission signals. Identifying dormant bugs requires non-linear junction detectors that find silicon components regardless of power status. This process neutralizes threats emitting electromagnetic radiation.
Properly executing technical surveillance counter measures prevents hostile entities from capturing sensitive boardroom discussions. Effective countersurveillance techniques rely heavily on specialized optical tools designed to reflect hidden camera lenses.
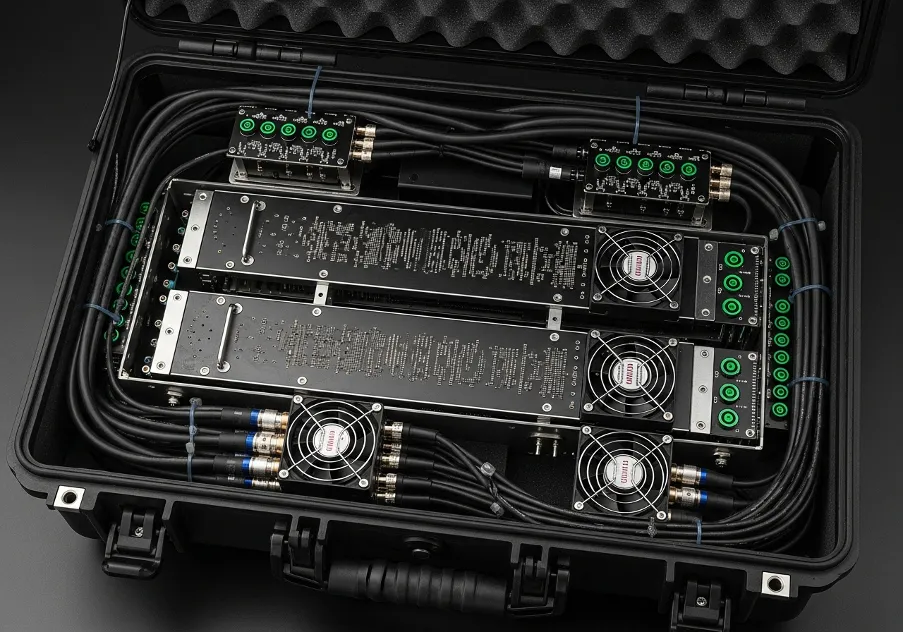
Security teams use the following hardware for technical sweeps:
- radio frequency sweepers;
- non-linear junction detectors;
- thermal imaging cameras;
- optical lens finders.
Deploying these tools regularly ensures physical spaces remain free from covert listening devices. Equipment calibration dictates the success rate of finding micro-transmitters hidden inside standard office furniture.
Surveillance Detection Routes and Physical Observation
Moving assets safely requires analyzing physical environments for hostile entities. Operators design complex surveillance detection routes to force followers into predictable patterns. Driving through traffic-heavy roundabouts or over specific bridges creates opportunities for double sightings. Identifying the same vehicle multiple times confirms active tailing.
Security personnel utilize counter surveillance techniques to observe daily routines and spot anomalies in the operational theater. A hostile tail exposes the watcher through behavioral analysis, answering the practical question of counter surveilance application in the field. Observers look for hostile agents making critical positioning errors during their pursuit.
Evasion Tactics and Behavioral Adjustments
Individuals execute anti surveillance protocols to avoid hostile monitoring completely. Implementing anti surveillance techniques involves changing clothing rapidly or driving unpredictably to break a follower's visual contact. The core difference lies in the actor; anti-surveillance relies on the target themselves taking evasive action rather than utilizing third party operators.
Adversaries constantly look for targets practicing dry cleaning drills designed to shake off followers. Spotting a target actively using counter survellience methods alerts the watcher that their presence is compromised. Recognizing this shift dictates whether the operation continues or aborts.
Operatives implement these tactics utilizing specific methods:
- rapid wardrobe alterations;
- erratic transit scheduling;
- deliberate route deviations;
- temporary communication blackouts.
Executing these maneuvers successfully breaks the physical line of sight with hostile operatives. Maintaining an unpredictable daily schedule prevents adversaries from establishing a baseline pattern of life.
Securing Digital Communications and Finalizing Defense
Hostile entities intercept digital communications as frequently as they deploy physical tails. Utilizing encrypted communication channels prevents adversaries from capturing sensitive dialogue over cellular networks. Deploying robust surveillance countermeasures secures data transmission pipelines against unauthorized access. You must treat digital hygiene with the exact same rigor applied to physical space inspections.
A comprehensive security posture merges physical observation with network encryption to disrupt modern monitoring attempts. Mastering counter surveillance demands continuous adaptation to evolving adversary technologies and operational tactics. Maintaining this rigorous defensive stance protects intellectual property, neutralizes tracking hardware, and ensures personal safety in compromised environments.
Learn more about alternative systems and related products from Prodefence in Counter-Surveillance.
Trusted Worldwide
Operating in more than 50 countries, we provide cutting-edge defense solutions that ensure your safety to every corner of the globe.
Get Advice From Our Experts
Please complete the feedback form to gain exclusive access to our catalog showcasing models that are not available on our website
We’re here to assist you with any inquiries, support, or information you need. Whether you're interested in our defense products, looking to collaborate, or simply have a question, our team is ready to help.